How can businesses better protect themselves from the increasing volume and complexity of cyberattacks while preparing for the opportunities of automation and digitalization of industries – this is the burning question of the day and our goal is to raise awareness to help them address it. This article focuses where we see the most significant threats and opportunities emerging, and highlights the implications of the increasingly connected world, how global regulation is responding, the need to inject trust into cybersecurity, ways to protect ourselves from intelligent cyberattacks, and what we should do to close the skills gap in an environment starved for cybersecurity talent, yet overwhelmed by volumes of data.

The leading cybersecurity experts from TÜV have forecasted eight challenges that organizations will cope with in coming times. The forcast is based on a survey of TÜV Rheinland’s leading cybersecurity experts where inputs were collected from clients in Europe, North America and Asia.
Following are highlights of the 8 cybersecurity trends identified this year:
Trend 1: A rising global tide of cyber-regulation increasing the price of privacy
Data protection is a critical concern in an increasingly digital world and May 25, 2018 is a turning point for data protection in Europe. It marked the end of the transitional period for the EU General Data Protection Regulation (GDPR) as it becomes enforceable by law. It disrupts data governance and how information is protected for any organisation controlling or processing EU citizen personal data, and leads a growing list of emerging data protection regulations from around the globe.
Data protection is a critical concern in an increasingly digital world
As business undergoes digital transformation and becomes increasingly connected, cyberattacks continue to grow in both sophistication and volume. Recent highprofile cyberattacks have showed just how vulnerable organisations are. The ransomware WannaCry infected more than 300,000 computers across multiple organisations, countries, and continents in less than 48 hours. 87 million Facebook profiles harvested by political consultancy Cambridge Analytica is being dubbed one of the most consequential data breaches in history, rivalling the breach of financial records from Equifax. These attacks predict a dark future for privacy.
GDPR disrupts the data governance and how information should be protected
Increasingly, organisations must be able to prove that they are processing personal data in accordance with the legal requirements of this evolving regulatory environment. GDPR introduces a number of key components including extra-territorial reach over EU data, individual right, data privacy officers, notice and consent, restrictions on secondary users, privacy impact assessment, and data breach notification. These requirements are forcing organisations to rethink data governance, systems architecture, documentation and data loss prevention.
Failure to comply could result in fines of up to 4% of global turnover
The related business risk is material. In the event of noncompliance or contravention, the EU is envisioning sanctions amounting to four percent of the previous year’s turnover, or EUR 20m, whichever is the greater. Weaknesses in technical and organisational data security such as outdated encryption standards leave organisations vulnerable to these fines.
Many organisations are underestimating the extent of such requirements
Few organisations are going to be ready by the impending deadline. Most, having underestimated the extent of the requirements, are still developing their plan for GDPR compliance. Some have decided not to develop a plan, choosing instead to treat non-conformity as just another operational risk to be managed – perhaps doubting the seriousness with which the EU commission will enforce it. Others are not sure if the regulation applies. As a result, the majority of organisations are starting late with implementation.
An emerging list of data protection regulations from around the globe
GDPR is leading a global trend as European regulators are not alone in mandating greater accountability at the executive level. The USA, Argentina, Brazil, Switzerland, Africa, India and China – all are revising their data protection regulations. Many share similar concepts like informed user consent and data breach notification obliging organisations to notify the relevant authority and all affected data subjects when a breach occurs – an often costly exercise. Yet this also leads to fragmentation and emerging market barriers driven by territorial requirements for data protection and data flows across borders. For global organisations, this will make international operations an increasingly costly and complex challenge.
Trend 2: The Internet of Things drives the convergence of safety, cybersecurity and data privacy
Today, product development, time to market considerations, and technical power constraints leave IoT devices exposed by exploitation of critical vulnerabilities. The impact of data breaches now extends far beyond simple data monetization to kinetic threats to health and safety, as devices and systems are directly connected to open networks. It is widely accepted that the state of IoT security is poor and with over 500 connected devices expected to cohabit with us in our homes by 2022, these represent a major risk to safety, cybersecurity and data privacy.
Mirai proved that IoT devices can be effectively weaponised as botnets
On October 21, 2016 a massive Distributed Denial of Service (DDoS) attack hit DYN Inc. and temporarily disrupted much of the internet on the East Coast of the United States. It affected companies like Twitter, Spotify, Amazon, Netflix, Reddit, the Guardian, CNN, and the New York Times. Formed mainly of hacked IoT devices, the Mirai botnet was a wake-up call about the vulnerability of internet connected things to cyberattacks.
Commercial and technical constraints leave IoT devices vulnerable to exploits
Many IoT devices are fundamentally insecure, leaving product manufacturers and customers exposed to the inherent risk of cyberattacks. This should not come as a surprise as manufacturers are not in the business of cybersecurity. Instead, they are under increasing pressure to innovate faster than the competition, while protecting their margins. Ensuring devices are easy to produce, functional, connected and secure – while limiting power consumption to extend battery life – is a complex technical challenge leading to difficult trade-offs.
Vulnerabilities often reside deep in the product software stack
To save time and money, software developers use open source code libraries rather than reinvent the wheel for basic features. These 3rd party libraries can be a source of critical vulnerabilities. A good example is the Devil’s Ivy vulnerability, recently found in the gSOAP toolkit that is often used by manufacturers to connect their devices to the internet. It is estimated that over one million devices exist that are vulnerable to the Devil’s Ivy stack buffer overflow exploit.
The impact of data breaches now extends far beyond simple data monetization
We are increasingly living in one integrated digital system aimed at improving the quality of our lives. But consumers simply do not have the knowledge to protect themselves from these vulnerable IoT ecosystems. Product manufacturers who neglect cybersecurity and data privacy concerns are delivering their customers into the hands of cybercriminals. In a world of cyber-physical things, this is a threat to personal health and safety, not just personal information.
Hackable medical devices endanger patient lives
Last year, the FDA confirmed that St. Jude Medical’s implantable cardiac devices, including pacemakers and defibrillators, were vulnerable to cyberattacks. Attackers could gain control of devices via accessing the transmitter that reads device data and sends it back to physicians. Another example is that of a baby heart monitor where a nun encrypted Wi-Fi network between the monitor and sensor left it vulnerable to cyberattack. Attackers could take control of the system and monitor a stranger’s baby and stop alerts being sent to the parents.

Hackable cars leave passengers at the mercy of their attackers
In 2015, a team of researchers was able to take complete control over a Jeep SUV. The vehicle’s CAN bus was hijacked over the cellular network by exploiting a firmware updates vulnerability. The researchers were able to remotely speedup, slow down, and even steer the vehicle off the road. More recently, a new vulnerability in CAN protocol was reported that is not only nearly universal, but can be exploited while bypassing the auto-industry’s attempts at cybersecurity controls. It allows attackers to shut off critical safety and security systems including air bags, antilock brakes and door locks.
Trend 3: Operational Technology emerges as a frontline for cyberattacks
The industrial internet is already transforming global industry and infrastructure, promising greater efficiency, productivity and safety. To compete means to move process equipment online, often unwittingly exposing component vulnerabilities to cyberattacks. Manufacturing plants are targeted to obtain intellectual property, trade secrets and engineering information. Attacks on public infrastructure are motivated by financial gain, hacktivism, and national state agendas. Fear of a worst-case scenario where attackers trigger a breakdown in systems that underpin society, was highlighted this year at the World Economic Forum. Industrial systems are particularly susceptible to supply-chain attacks, adversaries have recognised this and are targeting them.
The industrial internet is transforming global industry and Infrastructure
For the past 15 years, the internet has been transforming the business to consumer relationship, democratising information-based industries such as media, retail and financial services. For the next 10 years, it is set to disrupt physical industries manufacturing, energy, transportation and agriculture. Dubbed the ‘Industrial Internet,’ the trend to integrate information and operational technology networks will bring unprecedented opportunities along with new risks.
To compete means to move process equipment online
For decades, measurement data has been used by industrial sectors to improve productivity and competitiveness, and to save energy. At its most basic level, current data is compared to historical data to determine how processes should be run. Analytics provide recommendations, enhancements, and warnings to support decision making. The next big step for industrial evolution is to move measurement data outside of the facility and into the Cloud. This way information from process equipment from all over the globe can be combined, leading to new opportunities for competitive advantage.
Fear of a ‘worst-case scenario’ is highlighted by the world economic forum
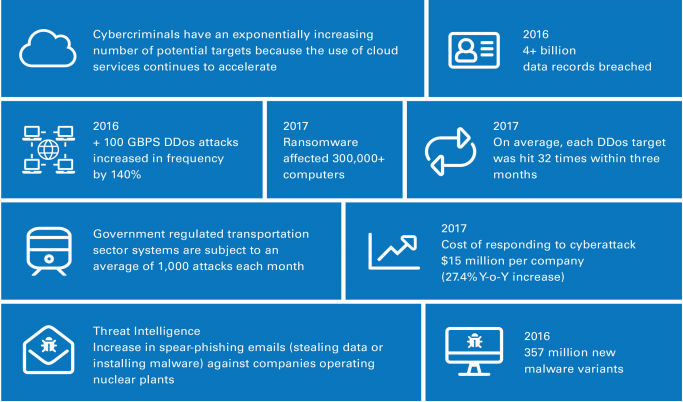
The volume and sophistication of cyberattacks is escalating, having almost doubled over the past 5 years. Historically, industrial systems were standalone and not connected to corporate networks or the internet, but in an increasingly connected industrial world, cybercriminals now have exponentially greater number of potential targets. As a result, there is a growing trend to attack critical and strategic infrastructure across the world including government, railways, banks, telecom- munications, energy, manufacturing and hospitals; raising fears that, in the worst case scenario, attackers could trigger a breakdown in the systems that keep society functioning.
Manufacturing plants are targeted to obtain trade secrets
As the volume of cyberattacks increases, manufacturing is becoming one of the most targeted industries. Just over a third of documented cyberattacks are targeting the manufacturing industry, with manufacturers appearing in the top three targets in five out of six geographies. This is because of the fierce competition in a sector where intellectual property is at a premium, yet investment in cybersecurity is lacking due to commercial focus on productivity and efficiency.
Public infrastructure attacks have destructive motives
Often overshadowed by the sheer scale of personal information being stolen by cybercriminals in the enterprise sector, cyber espionage groups are continuing to escalate their access to public infrastructure across the globe. For the past decade destructive attacks have been increasingly targeting a variety of organisations and critical infrastructure, but with a definite ‘spike’ in the past 18 months. The ‘Crash Override’ malware was used to attack the Ukraine power grid and was able to take control of grid circuit switches and breakers. More recently, attackers breached nuclear plants in order to map out computer networks and process control systems for future attacks
Targeting of supply chains is an emerging threat
Industrial processes depend on a regular supply of resources and logistical support. Attackers have recognised the importance of supply chains and have started targeting them with interception, infiltration, counterfeit and disruption. This can be demonstrated by the impact of cyberattacks on the global logistics industry. Last year, FedEx and AP Moller-Maersk reported combined business losses of nearly $600m after being hit by Ransomware and ‘Wiper` virus attacks. As supply chains become more global, the risks from intentional insertion of malicious functionality increase.
Additional budgets are required to address rising compliance requirements
In this context, organisations will need to allocate additional budgets to detection technologies and incident response, as opposed to prevention technologies only. Artificial intelligence (AI) and predictive analytics for cyber risk management of operational technology will be adopted. Compliance requirements from regulators to secure critical infrastructure will rise and increase the cost of compliance for operators. Regional and industry specific standards will bring clarity to the compliance regimen. Privacy regulations like GDPR will find its way into this domain where operators will be faced with a unique set of challenges around managing data protection and privacy especially with IIoT (Industrial Internet of Things).
Trend 4: With cyber defences in place, focus shifts to threat detection and response
Recent cyberattacks on high-profile organisations are proving that preventative controls alone are not enough against the sophisticated and persistent cybercriminals. Today, organisations take too long to detect a data breach. Due to the vast growth of security log data, limitations of incumbent technologies, ineffective use of threat intelligence, inability to monitor IoT devices, and shortage of cybersecurity talent, organisations are exposed to costly dwell times.
Organisations continue to take too long to detect a data breach
The faster a data breach is detected and contained, the lower are the costs and impact on reputation and business value. Cybercriminals take a matter of minutes to hours to compromise a network and extract basic data, or days to weeks to identify and steal critical data. However, organisations take on average 191 days to detect a breach and 66 days to contain it. Organisations that can get their detection time below 100 days can save over $1m. Furthermore, when a data breach is disclosed, stock price declines immediately by an average of five percent in line with customer confidence.
Traditional approaches to threat detection are cumbersome
Traditional approaches are built around security information and event management (SIEM) solutions. Unlike security cameras that go straight from installation to insight, traditional SIEM solutions are plagued with painful implementation, limited scalability, difficulty in integrating data sources, and convoluted reporting process. This is exacerbated by the fact that the amount of data analysed by security teams is doubling each year, and shifting towards unstructured.
The cyber security skills shortage is getting worse
I T organisations continue to cite cybersecurity as the biggest area where they have a problematic skills shortage. Looking back through the ESG’s annual global survey on the state of IT shows an alarming growth of the issue – more than doubling from 23% of organisations in 2014 to 51% in 2018. It is expected that there will be 3.5 million unfilled cybersecurity jobs by 2021. More than half-million of these are predicted to emerge in the U.S. The cybersecurity skills shortage is getting worse and there is no evidence to suggest it will slow down in the foreseeable future.
Rapid cyber-threat detection and accurate response requires a new approach
Modern malware and sophisticated cyber-threats require a proactive, agile approach to replace traditional SIEM solutions. Traditional solutions work to detect known threats within fixed enterprise network perimeters using signature-based techniques that are no longer effective. To materially reduce detection times and accelerate containment, organisations will increasingly adopt advanced security analytics. This new approach uses machine data to identify anomalies from a pre-determined baseline of usage behaviour across the dynamic landscape of the modern digital enterprise.
Barriers to effective use of threat intelligence remain
In an environment of ‘big security data,’ the combination of advanced threat intelligence and a team of security analysts can lead to actionable insight. Threat intelligence is not a technology but the knowledge about adversaries, their means, motives and intentions. It should be disseminated in a way that supports cybersecurity teams and the business to protect the critical assets of the enterprise. Yet, even the most cutting-edge threat intelligence is ineffective if you do not have the people with the knowledge, skills and experience to do something with it.
Trend 5: Increasing use of Artificial Intelligence for cyberattacks and cyber defence
As organisations undergo a digital transformation, there is a growing volume of increasingly sophisticated and persistent cyberattacks. With a global shortage of cybersecurity talent, organisations are losing the cyber arms race. The volume of security data now far exceeds our legacy capability to use it effectively, leading to a growing number of AIenabled cybersecurity use cases – accelerating incident detection and response, better identifying and communicating risks to the business, and providing a unified view of security status across the organisation.
Organisations are losing the cyber arms race
Gone are the days when cyber-attackers were little more than annoying ‘scriptkiddies.’ They have graduated to well-funded organised cybercrime and nation-state actors. They are a legitimate and sophisticated threat that regularly disrupts organisations and governments alike. Cybercrime is very lucrative, low risk and global. It is not as if the cybersecurity industry is standing still, the attackers do keep winning. So by leaving vulnerabilities un-patched, we are making it too easy.
The volume of security data now far exceeds our legacy capability to use IT
Most large organisations have deployed and potentially integrated dozens of security technologies. The digital economy is connecting everything to everything else, leading to billions of new endpoint devices. As a result, we are generating so much security event log and alert information, that it is no longer possible to see the forest from the trees. This is making the job of protecting the organisation increasingly difficult, and perhaps represents an even greater risk than the escalating sophistication of cyberattacks themselves.
The era of AI powered cyberattacks has started
AI threatens to exacerbate the already considerable cybersecurity challenge faced by organisations in an increasingly digital world. They are rare today, but we are seeing signs of AI-based advanced cyberattacks. Last year, we witnessed the first artificial intelligence based cyberattack where rudimentary machine learning was used to study patterns of normal behaviour within a company’s networks. Once a baseline was established, the malware began to mimic normal network behaviour to become almost undetectable.
Cybersecurity leaders will defend against AI attacks by using AI
The next-generation of cyberattacks will use AI-based malware capable of reacting in real-time to evade cybersecurity controls and necessitate new defensive approaches. Cybersecurity professionals are looking towards advanced cyber defences which use AI to pro-actively respond to such attacks. AI-based security automation can detect and contain the same incident within minutes. It is, therefore, increasingly considered a critical component in a modern cybersecurity strategy.
Turning to AI plugs the growing shortage of cybersecurity talent
Using AI security teams can quickly make sense of massive amounts of security data, putting alert information and event logs into far greater context. This ability to prioritise and focus on the highest risk threats holds great promise for organisations trying to protect their critical assets with scarce cybersecurity resources. This will, however, lead to some defensive roles (tier 1 and tier 2 security analysts, or security operations centre [SOC] analysts) to be at risk of being replaced by AI in the next 5-10 years.
Trend 6: Certifications become necessary to inject trust into cybersecurity
It is broadly accepted that cybersecurity and data protection are of critical importance in an increasingly digital world, but how one can judge the effectiveness of an organisation’s cybersecurity posture. For CISOs and product manufacturers alike, certification validates you have done what you say you have done. Today, however, product security assurance certification schemes tend to focus on the critical infrastructure and government sectors only.
Effective cybersecurity is needed for a viable IoT-based digital economy
With a growing share of services offered online, and the rapid proliferation of connected devices, it is increasingly apparent that cybersecurity plays a critical role in the viability of our digital economy. Protecting our digital ecosystems, from critical infrastructure to consumer devices must be a fundamental requirement for doing digital business. As a result, cyber-threats pose a serious risk to the fabric of contemporary society.
Leading to a growing concern for trust in cybersecurity
In fact, this year’s World Economic Forum Global Risks Report states that cyberattacks against businesses have doubled over the last five years. This year saw a significant jump in concern over cyberattacks and massive data fraud, with both ranking in the top five global risks by perceived likelihood. A Pew Research Center survey found that the majority (64%) of Americans have personally experienced a major data breach, and that many do not trust modern organisations to protect their personal information. The European Commission announced two initiatives related to certification and labelling – a security framework for ICT products, anda ‘Trusted IoT label’ giving information about different levels of privacy, security, and where relevant, demonstrating compliance with the directive on security of network and information systems (NIS Directive); adopted by the European Parliament in 2016.
Impacting the business ecosystems and supply chains
The ongoing digital transformation of business is leading to increasingly complex and networked ecosystems and supply chains, with the automotive industry being a good example. Here, the trusted information security assessment exchange (TISAX) audit is gaining traction. TISAX enables accredited providers to offer mutually accepted assessments based on the VDA (German Association of the Automotive Industry) information.
Security assessment which, in turn, is based on a catalogue of information security criteria incorporating key aspects of international ISO/ IEC 27001 and 27002 standards.
Certification validates you have done what you say you have done
With cybersecurity acknowledged to be of such critical importance, a key question arises how you can judge the effectiveness of an organisation’s cybersecurity posture. The existence of corresponding certification plays an important role, for example, in making a decision on whether to impose administrative fines, and on their amount. A certification procedure can prove that the provisions of a new regulation have been observed and implemented in full.
Regulated certification schemes lag the market need
The concept of a security certification framework for products and services is a good one, but these should be done at a global level, if at all possible, and in such a way not to give a false sense of total security. National level schemes, for example, that define standards and evaluation methods and only recognise certification bodies within their own territory would create market inefficiencies. Recent experience with common criteria has shown that even if a pan-region approach is achieved, global support is required to avoid multiple regional certifications for one product.
Consumers need easy to understand transparent information
Independent product evaluation can be a very resource intensive process and so tends to focus on high risk government or critical infrastructure products and services. This gives rise to process-based approaches including ISO/ IEC 27034, as well as certifications for specific types of systems such as ISA/ IEC 62443. But with pressure for even faster, cheaper product development lifecycles, agile assessment schemes, utilizing test automation environments will need to be created and evolved.
Trend 7: Passwords being replaced by biometric authentication
Our digital lives are ruled by a complex web of online apps each requiring a user name and password to control access. To protect the data behind these apps, selecting an obscure and complex password, and changing it often, is good practice, but it is quite rare. With exponential improvements in computing power, and easy access to lots of it in the cloud, the time it takes to brute force passwords is rapidly reducing. What took nearly 4 years in 2000 now takes only 2 months. Add to that the fact that stolen, hacked and traded passwords have never before been so openly available. As a result, it is increasingly commonplace to encounter biometric authentication (facial, fingerprint, iris and voice) included in everyday mobile, tablet and laptop devices, as well as physical access and online services.
Password best practice is well known, but frustrating to follow Traditional best practice
Traditional best practice approaches to creating passwords has made us lazy. Making use of irregular capitalisation, special characters and numbers, and then being forced to change it every 90 days lead to passwords like ‘P@ ssW0rd123!’ Such passwords are hard to remember but relatively easy to guess. When faced with logging into an application after an extended period of time, it is frustrating to reset your password because you have forgotten it. The issue is that most people tend to use the same techniques when crafting passwords that leave them predictably vulnerable to password cracking algorithms that target those specific weaknesses.
Moore’s law renders passwords weaker over time
Over time passwords weaken dramatically as computing power doubles every 18 months, and cybercriminals become more proficient. For example, a password that would take over three years to crack in 2000 took just over a year in 2004, and five years later in 2009 just 4 months. In the modern era, passwords simply do not stand up against sophisticated cyber-threats. A third of cybercrime originates from stolen passwords, and over 1.5 billion passwords have been stolen.
An emerging theme from recent data breaches points the finger squarely at passwords
In many of the recent headline-grabbing data breaches, the attack vector has been a common password. This is not surprising how many people reuse passwords between accounts. For example, the breach of a White House contractor was made possible by him reusing the same password as his gmail account, which turned out to have been stolen during the Adobe breach in 2013. In fact, as many as two-thirds of data breach incidents are a result of leveraging weak, stolen or default passwords, and nearly all phishing attacks are after user credentials.
Biometric authentication determines exactly who is accessing a system
Biometric authentication creates accountability. Every access or action is recorded along with the individual associated with it. This naturally reduces the risk of misuse, fraud and data leakage. Within the next few years, three biometric options will become standard features in every new phone – a fingerprint scanner built into the screen, facial recognition powered by high-definition cameras, and voice recognition based on a large collection of a human vocal sample. The number of fingerprint reader-equipped devices has already passed a billion. Unlike passwords, there is no way for someone to forget his or her biometric credentials, and this information is very difficult to forge. On the downside, if the biometric credentials are ever compromised, it is very difficult to alter one’s fingerprint or their appearance.
Trend 8: Industries under siege: Healthcare, Finance & Energy
The majority of cyberattacks are undertaken by criminal organisations and are motivated by money. The value of information on the dark web depends on demand for the data, the available supply, its completeness and ability for reuse. As a result, healthcare and financial personal information are highly sought after. Medical records can fetch $1-$1,000 depending on how complete they are, while credit cards can fetch only $5-$30 dollars, if bundled with the information necessary to do immediate damage. Other cyberattacks have more political and nation-state motives.
Medical industry: Versatile challenges – growing spending
In 2017, cyberattacks struck hospitals and health systems at an alarming rate and the cybersecurity exposure is still growing. With the increase in the digitalization and use of healthcare information, the availability of consumer access to private health information (PHI), continued innovation and availability of consumer-focused health applications and devices as well as the growth of networked medical devices, the cyber exposure in the healthcare industry will rise. The challenges of cybersecurity in the healthcare sector are also versatile. Whether it is malware that compromises the integrity of systems and privacy of patients, or Distributed Denial of Service (DDoS) attacks that disrupt facilities’ ability to provide patient care, cyberattack scan have other results than only financial loss or the breach of privacy – the direct impact on human lives. Patient safety, financial loss, disruption of health services, reputation damage, and exposure to litigation related to cyberattacks remain the key risks for the medical industry in 2018. Organisations spend more to protect their systems and patient data. Cybersecurity Ventures predicts global healthcare cybersecurity spending will exceed $65 billion cumulatively over the next five years, from 2017 to 2021.
Financial sector: Increased volume and complexity of attacks
The area of financial services is relatively well-developed in terms of cybersecurity. This is also largely due to legal regulations especially in regard to risk management. Nevertheless, 2017 was a game changer. We saw an increased volume and complexity of cyberattacks due to the growth of cybercrime services in which advanced attack capabilities are sold to and leveraged by less sophisticated adversaries. Reported cyberattacks against financial services firms rose by 80 percent in the last year, reflecting the increasing number of attacks aimed at organisations. The risk of cyberattacks is also being amplified by the significant outsourcing done by investment dealers and asset managers.
Different attack vectors: One goal – money
Different cybercriminal groups penetrated bank infrastructures, e-money systems, crypto-currency exchanges, capital management funds, and even casinos, in order to withdraw large sums of money. In this context, the interception of bank customers’ electronic operations through the hijacking of bank domains in order to perform phishing attacks, install malicious code and wield the operations of customers who were using online banking services at the time appear already traditional. The main key events were continuous cyberattacks targeting systems running SWIFT, which affected several banks in more than 10 countries around the world. In addition, cybercriminals have been actively using ATM infections including those on financial institution’s own networks and PoS terminal networks to change card balances. Attacks on ATMs became so popular in 2017 that the first ATM malware-as-a-service was offered.
New unknown risks as a result of open banks eco-systems
In the future, it is expected that the financial sector will suffer further. Unknown risks will also arise as a result of the demand for further opening of banks’ eco-systems. Moreover, significant reputational damage is expected for financial organisations, when banks and insurers are forced to reveal any data breaches that occur in the context of the GDPR. The customer trust in banks and insurers still remains high, with 82 percent rating them among the most trusted institutions, may be due to the practice that financial organisations fail to voluntarily share news of data security breaches.
The great cybersecurity opportunity for financial organisations will be to cooperate and co-ordinate across the financial sector involving insurance, banking and security firms.
Energy sector: Attractive target due to its national and economic importance
The energy sector will be the prime target for cyberattacks, particularly companies engaged in alternative energy development, coal mining, nuclear energy development, natural gas distribution, oil and gas exploration and production, oil and gas field equipment manufacturing as well as oil and gas field services petroleum refining.
New quality of attacks
Classical data stolen from energy companies includes business process information, contract negotiations information, executive communication, market analysis and proprietary technologies. In 2017, Dragonfly was synonymous with a new wave of cyberattacks that could provide attackers with the means to severely disrupt affected operations. But the nature of attacks is changing. According to sources of the New York Times, hackers compromised computer systems at a petrochemical plant in Saudi Arabia in August 2017, aiming to not only destroy or steal data but to cause a deadly explosion – a new quality of an attack that could be replicated in other countries because the compromised systems are used in thousands of industrial plants worldwide. One of the recent events was in April 2018 when the energy industry of the UK was on alert for cyberattacks on UK power network. In this context, more and more governments worldwide are considering ways to optimise the police protection of critical infrastructure such as nuclear sites. A regulatory framework for cybersecurity in critical sectors is due to be implemented by May 2018 in the UK.
Serious impact on general supply security
The cybersecurity risks will grow. A decentralized energy supply system requires a distribution network which is nolonger based on conventional perimeter security. Smart grids represent a large number of gateways for advanced persistent threats and DDoS attacks. Increasing pairing of mobile private devices with low perimeter security involves considerable malware risks e.g., in the case of WannaCry, which may also have serious impacts on the common good and general supply security.

By Norman Hübner – Press Officer IT, Telecommunications & Information Security, TÜV Rheinland