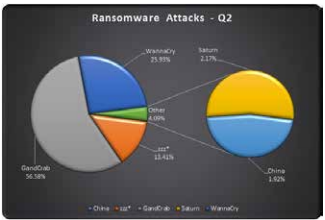
Last year WannaCry created havoc across the globe, and due to its lateral movement, it penetrated into the networks and skipped across the countries and continents. The security community has been highly proactive in 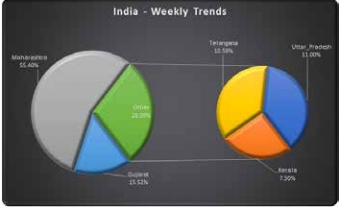 taking down the infrastructure associated with WannaCry, however, due to its ability to move across networks, eScan observes that it still exists in its dormant form.
taking down the infrastructure associated with WannaCry, however, due to its ability to move across networks, eScan observes that it still exists in its dormant form.
eScan’s telemetry servers have been picking up reminiscent artefacts of WannaCry ransomware on regular basis. Over the period of last few months, they have observed a steady decrease of incidents involving WannaCry, and hopefully by the year end WannaCry should meet the same fate as that of Conflicker worm/ DNS changer botnet.
eScan has been observing various variants and newer ransomware being added into the family, however very few of them have shown active development viz., GandCrab and ZZZ. In the last few weeks, GandCrab has taken center-stage and is evolving at a much faster rate, which suggests that the ransomware developer/ criminal nexus is growing stronger and many of the criminals are now switching their loyalties to GandCrab. It is a sheer fact that the developers are taking keen interest and adding numerous weapons to its arsenal.
The next step of the evolution for ransomware would be Crypto miners with Info stealers and a ransomware – all bundled into one.
India has seen its share of ransomware attacks and Maharashtra is leading the way for the week, however, in states like Gujarat, Telengana, Uttar Pradesh and Kerala eScan has observed a rise in activity of the GandCrab ransomware attacks, and xtbl, korean, Dharma and CrySiS variants of ransomware family are making rounds.
Prevention measures
- To stay safe from such ransomware attacks, all the organizations and users need to ensure that the patches released by Microsoft have been updated or patched immediately
- Administrators should block all executable files from being transmitted via e-mails.
- Administrators should isolate the affected system in the network.
- Administrator can restore the encrypted files from the backup or from system restore point (if enabled) for affected systems.
- Install and configure eScan with all security modules active: o eScan real time monitoring. o eScan proactive protection. o eScan Firewall IDS/IPS intrusion prevention.
- Users shouldn’t enable macros in documents.
- Organizations should deploy and maintain a backup solution.
- Most important, organizations should implement MailScan at the gateway level for mail servers, to contain the spread of suspicious attachments.