We are in the early stages of a wave of artificial intelligence (AI) and quantum computing that will change the security landscape as we know it. It is an inflection point that will force the reinvention of workflows, operating models, and the assumptions that security practitioners have relied on for years. Many emerging professionals have only ever known a tool-first culture, and many of the leaders who built the earlier frameworks are no longer here to pass down their reasoning. Yet the velocity of threats continues to increase. Technology amplifies their impact.
In times like this, there can be the temptation to seek the easy route – the allure of the latest miracle tool. Each new platform arrives with a promise of transformation, and each new dashboard is perceived as the breakthrough the sector has been waiting for. However, as the field pursues these solutions, it may unintentionally stray from the first principles that once anchored it – understanding the fundamentals of why the security function exists, what it means to protect, and how security should integrate with the mission of an organization rather than operate as an isolated technical function.
The result is an industry facing significant challenges – oversupplied with tools, lacking a strategic presence at the executive level, and struggling to articulate its value to the very organizations it was designed to safeguard. The way to overcome these challenges is to anchor back into first principle thinking. Without a clear return to these foundational concepts, organizations risk building security programs that are fast, modern – and fundamentally misaligned with their mission.
With access to 175 years of archives, Pinkerton has reflected on lessons within the security industry and is positioned to lend a unique perspective on the past, present, and future. The last time the world faced a transformation of this scale was during the 1820s, when railroads and steam power carved out the routes that would underpin modern transportation and commerce – and subsequently, the security industry itself. At the center of this change was Chicago, Illinois, a burgeoning village on the southeastern shore of Lake Michigan that transitioned to an industrial and railroad hub by the 1850s.
As the trains converged and the population surged, so too did the undercurrent of crime. In this crucible, Allan Pinkerton, founder of Pinkerton’s National Detective Agency, established a pioneering detective and security force laying the foundation for modern private security and law enforcement practices.
The advent of AI and quantum computing represents a shift of similar magnitude. AI is laying down new lines that will dictate how people, information, and threats travel, redrawing the terrain once again. To survive this next phase of evolution, security leaders must reconnect with the humanistic core of the profession. They must understand the root causes they are protecting against, the objectives their organization is truly pursuing, and the value that security preserves.
Lessons learned
Pinkerton and Lincoln: The origins of modern security
Pinkerton’s approach to intelligence and security is grounded in values that have defined the Agency since its founding – values demonstrated in Allan Pinkerton’s work alongside Abraham Lincoln. The partnership between Pinkerton and Lincoln began in 1855 in Chicago, Illinois, 13 years after Pinkerton immigrated to the United States. Lincoln, then a railroad attorney, drafted an agreement between Pinkerton & Co. and seven Midwest railroads that led to the establishment of the Northwestern Police Agency, later named Pinkerton’s National Detective Agency.
Securing such a significant agreement was indicative of an already well-established and formidable reputation Pinkerton had for the pursuit of justice – he had already survived at least two assassination attempts from a couple of bad actors who didn’t like how Pinkerton derailed their nefarious schemes.
Chicago was one of the fastest growing cities in the country and the hub of ten trunk lines, with 58 passenger trains and 38 freight trains arriving daily. It was said that the Illinois Central Railroad was the first great ‘St. Louis cut-off’ – a trip that could be made between Chicago and St. Louis in 24 hours. Chicago became ‘The Queen of the West,’ the first stop for many traveling to the western frontier. It had also earned an unenviable reputation for crime. The agreement, detailed and forward-thinking, laid the ground work for a long and trusted professional relationship.
Executive Protection for the Highest Office
By 1861, the country was on the verge of fracture. Rumors of secession and violence swirled around Lincoln’s election, and reports of an assassination plot surfaced as he prepared to travel to Washington, D.C., for his inauguration. At the end of January 1861, S.M. Felton, the President of the Philadelphia, Wilmington, and Baltimore Railroad, wrote to Pinkerton asking him to investigate threats along the line. By February 3, Pinkerton and a team of his best detectives – Kate Warne (Pinkerton’s, and likely America’s, first female detective), Hattie Lawton, Timothy Webster, Harry W. Davies, and Charles D.C. Williams – had launched an in-depth investigation, traveling to critical junctures along the railroad.
Pinkerton and his operatives confirmed that a group in Baltimore planned to attack Lincoln’s train during its scheduled stop. Acting on that intelligence, Pinkerton quickly developed a plan to change the route and conceal the President-elect’s travel. Late on February 22, 1861, Lincoln boarded a night line train in Philadelphia, accompanied by Pinkerton, Warne, and George H. Bangs, the Agency’s first Superintendent and General Manager. Traveling quietly under the cover of night, the group arrived safely in Washington, D.C. at dawn on February 23. On March 4, Lincoln took the oath of office as the 16th President of the United States.
The Baltimore operation became a model for modern protective intelligence. By combining research and intelligence with clandestine tactics and well-orchestrated maneuvers, Pinkerton not only ensured the President-elect’s safety but also established a legacy of intelligence and security operations that would become the hallmark of his agency.
The birth of the secret service
When the Civil War began in April 1861, Lincoln again turned to Pinkerton for help. Under the alias Major E. J. Allen, Pinkerton led the Union Intelligence Service, the forerunner to the United States Secret Service. Working with General George B. ‘Little Mac’ McClellan, his team gathered field reports, verified intelligence, and provided insights that informed command decisions – methods that became the model for federal intelligence practices that followed.
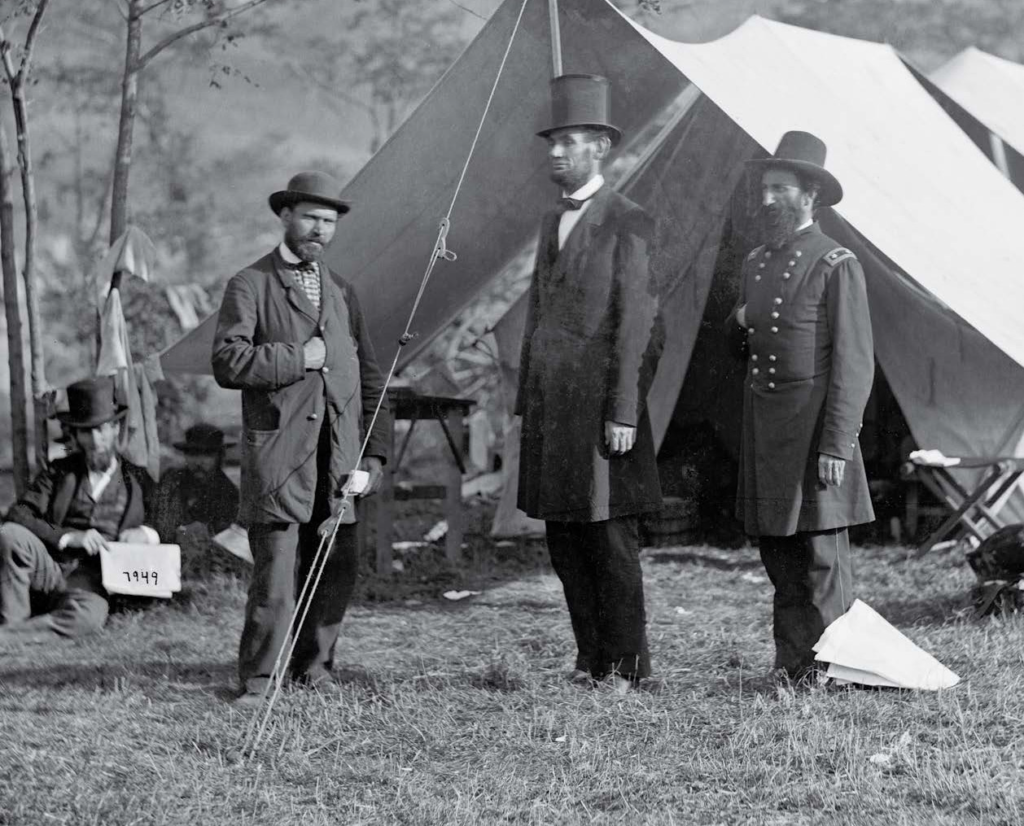
In 1862, during the Maryland Campaign, Pinkerton moved his headquarters to the battlefield at Antietam to maintain close coordination between intelligence and command. When President Lincoln visited the site after the battle, he stopped at Pinkerton’s tent. A photograph taken that day, showing Lincoln with Pinkerton and General John A. McClernand, became one of the war’s most recognizable images, serving as a testament to the partnership that shaped both the war effort and the future of protective intelligence.
For Pinkerton, his work with Lincoln proved that proactive intelligence could alter the course of history. His scouts and spies played a decisive role in supporting the Union Army, gathering data that provided a tactical advantage on the battlefield. Their work on the ground – through reconnaissance, surveillance, and verification – laid the foundation for modern intelligence operations.
Evolving tools, enduring principles
In the security profession, there is a tendency to confuse speed with progress. The last few decades have seen a flood of new platforms, software, data sets, and dashboards, each promising smarter, faster, more effective security. Yet human behavior – and the threats and risks that stem from it – has remained remarkably consistent throughout history and across the globe. Technology has simply increased the velocity of those threats.
Technology has always been a part of Pinkerton’s work. The company’s early intelligence reports and wanted posters were tools of data management long before the term existed. But our mission has never been about the tools themselves. It has always been about protecting people, property, and objectives. For us, these are the constants in an industry that has changed in scale and pace, but not in its underlying nature.
Many organizations have invested heavily in technology but still struggle to manage threats effectively. This is partly an issue of integration and fragmentation, said Pinkerton Vice Chairman Tim Williams, who started in the security industry in 1979.
“One of the most concerning issues to me is that, even today, after all we’ve learned, all the studies that have been conducted, and all the research that has been done, corporations still don’t tend to organize effectively or efficiently to manage potential threats. Security is still viewed in very disparate ways: fraud investigations are often handled by internal auditors, counterfeiting by the legal department, while physical security may rest with facilities,” he said, “When these groups don’t exchange information or agree on what’s most critical to share, a lot of risk slips through the cracks. Because of this, some companies – even very large, successful companies – are still flying somewhat blind. These organizations are not sharing the information they need to, and that lack of coordination becomes exponentially more dangerous when an organization is facing an escalating threat.”
In a stark example, there is a case where a single employee triggered three separate investigations – one for fraud, another for a personnel issue, and a third for suspicious IT activity. Each department – audit, HR, IT – was working in isolation. None realized they were tracking the same person. By the time they connected the dots, the damage had already been done.
Williams stated that planning for yesterday’s crisis is one of the most common and costly mistakes companies make. “Organizations often avoid planning for worst-case scenarios because the process is uncomfortable. Real risk isn’t always the event,” Williams said, “It is the blind spots – the institutional fragmentation that allows it to unfold unnoticed. Integration is no longer optional. It’s the baseline.”
Objectives, tactics, and tools
At every level, security needs to be rooted in understanding what the organization is trying to achieve before deciding which tactics and tools to apply. Without clear objectives, organizations tend to accumulate disconnected technologies that increase complexity while leaving the core problem unsolved.
“It’s not uncommon for an organization to contact us and say, ‘We need to implement a GSOC because everyone else has one,’” said Jack Zahran, President of Pinkerton, “In those moments, the role of the security professional is to pause and ask, ‘What are you trying to achieve? What’s the objective behind it?’ Risk exists everywhere, but not all risks are relevant to every organization.”
As Zahran notes, threats in the market such as cyber intrusions or physical breaches, do not impact all organizations uniformly. Their relevance and severity depend on the specific context of the organization’s aims. Similarly, not every tool or technology is suitable for every organization. The value of a specific technology will depend on whether it meaningfully advances the organization’s goals. A financial institution pursuing rapid digital expansion might prioritize defenses against data exfiltration to protect customer trust and regulatory compliance, whereas a manufacturing firm focused on supply chain efficiency could emphasize resilience against disruptions to production lines.
“Grounding an organization’s approach to security in its core objectives ensures that strategies remain aligned with business priorities,” Zahran added.
The benefits of this design philosophy are multifaceted. It facilitates early detection of weak spots through proactive risk assessments grounded in objective alignment, allowing for mitigation strategies that are both efficient and scalable. Moreover, framing security as an integral component of value protection – rather than a mere cost center – fosters a return on value that transcends conventional return-on-investment (RoI) calculations. The focus should accordingly shift to measuring return on value. This perspective ensures security is optimally aligned with preserving and enhancing organizational assets, reinforcing its strategic relevance.
A through line of first-principles thinking
Across the industry, much of what is marketed as innovation has drifted away from the fundamentals of security. New certifications, buzzwords, and predictive systems often promise foresight but deliver complexity. The result is a field in danger of mistaking software for strategy.
Our Agency got its start on railroads and stagecoaches, protecting business continuity along routes that powered commerce. Pinkerton operatives rode shotgun (we quite literally created the term) on those overland routes, safeguarding people and products in transit. The work required clarity of purpose, discipline in execution, and a firm grasp of the client’s core objectives.
After 175 years, the principles that grounded our earliest work are still as relevant as ever. The tools have changed, the fundamentals have not. The same first-principles thinking that informed Pinkerton’s railroad operations now guides how we support global supply chain logistics. The same instinct to distill, catalog, analyze, and verify information serves as the basis for the digital intelligence systems we build. Pinkerton’s philosophy favors simplicity over complexity – identifying the clearest, most direct path to understanding objectives and managing risk.
Objective-led design and value-based security
Objective-led design and value-based security are complementary approaches to security that tailor protective measures to organizational priorities. Both move beyond traditional, reactive security models to create frameworks that enhance resilience and mission success.
Understanding how objective-led design and value-based security work in practice is key when supporting a client’s needs. Every organization has different goals – securing a new location, expanding operations, launching a new product – and a security professional must understand their value. First-principles thinking deconstructs these objectives, identifying vulnerabilities and opportunities where security can enable progress toward the organization’s ‘North Star.’ Each of these goals or objectives presents a different mix of risk requiring solutions that integrate seamlessly with mission-critical activities. Once objectives have been outlined, risk has been calculated, and operations have been planned, value-based security steps in. An organization may have more than one objective that is deemed highly valuable. It is up to the security professional to protect and measure these objectives closely as a return on value. Consider insurance, for example, and the policy chosen for an individual’s home. A homeowner’s objective is to feel safe in their space in case of an emergency or accident, so they invest in insurance to secure their objective. They may live in their home for 30 years, pay monthly insurance, and have minimal to no incidents. The return on value? Living in a home unafraid of costly disruptions – objective achieved. If you consider security as insurance, the essence remains – know the value of the objective and feel confident in the return on value.
When risk is viewed as anything that can disrupt an organizational objective, the question becomes not ‘What will this cost?’ but rather ‘What is the objective?’ and ‘What is the value of protecting this objective?’ Understanding the relative value of each objective helps organizations allocate resources effectively and identify vulnerabilities sooner that could undermine success and profitability.
Despite their different lenses, objective-led design and value-based security share key similarities. Each approach shifts security from a standalone function to one integrated with organizational goals. Objective-led design ties security to specific objectives, while value-based security emphasizes protecting the broader value those objectives create. Both approaches diverge from conventional RoI metrics, focusing instead on mission success and the preservation and enhancement of organizational value. Both are proactive in nature, emphasizing early identification of vulnerabilities. And both advocate for solutions grounded in organizational context. For example, a technology firm might design security to protect intellectual property, while a manufacturer might prioritize physical safety. In either case, the goal is to protect what drives the organization’s value.
Implementing objective-led design and value-based security
Implementation of objective-led design requires a deep understanding of the organization’s strategic goals and close collaboration with leadership to define the master objective. Security professionals should conduct a root-cause analysis to map threats and vulnerabilities against these goals, selecting tools and behaviors that scale with the organization’s mission. This approach excels in dynamic environments where specific objectives drive competitive advantage.
Organizations adopting objective-led design often experience enhanced agility, as security becomes a collaborative partner in pursuing excellence, rather than a reactive barrier. For example, a global tech company aligns its security goals with its strategic aim of technological leadership and data security. By conducting analyses and recalibrating security measures facing dynamic market conditions, the company seamlessly integrates security into product development. This proactive approach strengthens internal and external collaborations, transforming security into a partner in innovation. Over time, this approach strengthens long-term relationships within the organization, positioning security as a trusted ally in navigating crises and sustaining growth.
Implementing value-based security involves a wider assessment of what constitutes value within the organization, including tangible assets such as infrastructure, as well as intangible elements such as stakeholder trust and brand reputation. Implementation begins with identifying all value drivers, then designing security measures to protect them holistically. For instance, a hospital might prioritize patient data security and physical safety to maintain trust and compliance, viewing these as critical to its value proposition. A pharmaceutical company also prioritizes patient data security and the safety of its research processes. A data center company focuses on the security of stored data and the integrity of its infrastructure. In retail, ensuring customer data protection and a secure shopping environment are among central values.
This approach is particularly effective for organizations with diverse stakeholders or complex operations, though it may demand broader coordination and resource allocation to manage the scope of risks.
Integrating for impact
In practice, objective-led design and value-based security are not mutually exclusive – they should be implemented in tandem for greater impact. Objective-led design provides the tactical framework, aligning specific security measures with organizational goals. Meanwhile, value-based security offers the strategic lens, ensuring those measures collectively protect the organization’s broader value. For example, a financial institution might use objective-led design to secure digital transformation initiatives (a core objective) while employing value-based security to safeguard customer trust and regulatory compliance (key value drivers).
Ultimately, objective-led design and value-based security both advance an organization’s evolution from reactive to strategic, aligning protective measures with organizational priorities. Objective-led design excels in precision, grounding decisions in first-principles analysis; value-based security provides the holistic view needed to preserve value across multiple dimensions. By understanding their complementary strengths, security professionals can craft integrated strategies that mitigate risks, enable mission success, and reinforce the intrinsic role of security as a trusted partner in organizational resilience.
“These approaches, integrated together, embody a paradigm shift toward strategic integration, equipping the security industry with a resilient framework for addressing the complexities of modern threats,” said Zahran, “Over time, their long-term relationships are strengthened within the organization, positioning security as a trusted ally in navigating crises and sustaining growth.”
Humans in the loop
Williams reiterated, “The top threats to societies and corporations really haven’t changed. We’re seeing the same challenges today, just in greater volume both in crime and in information.”
One of the greatest challenges facing the industry today is making sense of the vast amount of information out there and knowing how to synthesize and analyze that intelligence – aligning it with clear principles and a disciplined, human-led process.
Technology alone cannot solve this issue. Instead, what’s needed is a shared understanding of organizational objectives and a system that ensures the timely flow of critical information across teams. Ultimately, effective threat management depends less on the sophistication of tools than on how well an organization aligns its people, processes, and intelligence to its specific operating environment.
Principles in practice: Pinkerton’s EPIC framework
Pinkerton has evolved alongside society, continually adapting to meet the ever-changing security needs of each era. From pursuing outlaws and bank robbers during the expansion into the western frontier, to combating counterfeiters before and after the establishment of federal currency, testing hotels for illicit behavior during prohibition, providing onsite protection during the World Wars, and innovating when needed to stay a step ahead – just to name a few. Our services have always been adaptable, tailored to meet our clients’ needs. And here we are in 2025.
Pinkerton organizes its work around the EPIC framework – four service lines that allow us to address the unique mix of risks and priorities each organization faces and create solutions that are both flexible and effective: Embedded Subject Matter Experts (SMEs), Protection, Investigations, and Consulting. Together, these pillars show how we put our long-standing security principles into practice.
Embedded Subject Matter Experts (SMEs)
Placing seasoned experts directly within an organization ensures deep alignment with its culture, operations, and objectives. This integration accelerates decision-making, strengthens internal capabilities, and turns expert guidance into lasting, actionable results.
Protection
Physical security services – including executive protection, secure transportation, event security, and onsite and residential programs – provide consistent, professional safeguarding of people, property, and operations, delivering the confidence that critical risks are actively managed.
Investigations
Rapid, discreet, and thorough investigative support – spanning due diligence, fraud examinations, threat assessments, and internal matters – uncovers facts quickly, minimizes reputational and financial exposure, and equips leadership with clarity to act decisively.
Consulting
Strategic advisory that identifies emerging risks, designs resilient security programs, refines policies, and facilitates scenario-based exercises. The focus is on building sustainable risk management capabilities so organizations emerge more prepared and resilient.
Equally important is the discipline to operate without technology at all. Kyle Dukes, Managing Director of Information Systems and Technology at Pinkerton, said, “Within Pinkerton, a question we often ask is, ‘What if we lost it all?’”
Beginning in the 1850s, Allan Pinkerton standardized operative reports and case documentation, creating a systematic approach to intelligence gathering. In 1871, the Great Chicago Fire destroyed the Pinkerton office building and most of the Agency’s early records, including 59 volumes of Secret Service files, Pinkerton Protective Patrol nightly reports since 1856, and every issue of the Chicago daily or weekly newspapers since 1854.
When they lost it all, the Agency was resilient and developed something even better – a comprehensive criminal identification system that combined a photographic ‘Rogue’s Gallery’ with a cross-referencing system for criminal records. This innovation enabled the tracking of suspects across state lines and pioneered data management techniques that would directly influence federal law enforcement identification practices decades before standardized national databases existed.
“If every system went offline – if all that we had to work with was pen and paper – could the work continue? The answer must always be yes,” said Dukes.
Pinkerton and his team understood the objective. At its core, security is not a product or a platform. Security is the act of safeguarding another person, asset, or interest.
A strategic approach to technology
By the 1960s, the Agency’s name had become a part of the language – wherever security measures were needed, a ‘Pinkerton’ was understood to mean an armed guard – and yet, many ‘Pinkertons’ were in fact electronic gadgets. The Agency developed technology that covered everything from protection against breaks, industrial espionage, and pilfering by employees to fire protection – with electronics cast in a starring role. Even then, with the advancements to electronics cast in a starring role. Even then, with the advancements to fight and prevent crime, they understood that well-trained, experienced people were still the basic ingredient.
“You can have all the proper tools and technology in place, but without an analytical mind to digest that information and make sense of it – turning it into something meaningful that the client can understand – it’s largely useless,” said Chris Morton, Managing Director, Northwest Region, “AI, for example, is a great tool that can speed up the process of collecting data. However, it still takes human analysis and expertise to assemble that data into a useful report. That’s the value that is sometimes missed in our industry: transforming raw data into a usable tool, something that the client can act on.” Technology is a means of returning to the principles that have guided the profession since Allan Pinkerton’s time, uniting people, process, and technology into one operational system.
“Every tool we use is designed to serve a clear objective, augmenting or accelerating our work,” said Dukes, “In the field, Pinkerton’s proprietary technology gives clients near real-time visibility into events as they happen. Through mobile reporting, agents can transmit formal updates – complete with images, notes, and videos – directly to client stakeholders.”
That immediacy allows for faster decision-making, but it also builds trust. Rather than receiving an after-action summary days later, clients are able to understand the full context of an event as it unfolds and can feel confident that our on-the-ground agents are actively managing the situation.
We follow the same approach to integrating technology into our investigations. Automation allows us to gather and cross-check data, something that once took days (or weeks) of manual effort. However, it takes human expertise to validate and contextualize that information. Our analysts verify sources, confirm identities, and synthesize findings into actionable reports that our clients can use.
Proprietary tools such as the Pinkerton Crime Index (PCI) provide this integration of data and human expertise. By aggregating regional crime data, PCI helps forecast neighborhood-level crime risk and identify emerging threat patterns. These insights support concrete business decisions, whether that’s determining proper staffing levels, selecting a safe travel route, or evaluating a new location. Having a shared baseline of region-specific data allows Pinkerton teams and clients to work from the same facts when discussing exposure, risk appetite, or investment priorities. The outcome is a more informed, data-driven conversation where technology supports and enhances human insight and experience.
This balance of technology and human expertise drives Pinkerton’s work at the enterprise level – providing consistency and the same standard of service anywhere in the world. Our internal systems help keep vendor vetting, pricing, and compliance consistent worldwide, reducing friction and ensuring a uniform standard of quality.
Conclusion
Our founder, Allan Pinkerton, was often described as indefatigable, tireless in his pursuit of justice. He said, “Crime never sleeps,” which led to the creation of our motto, “We never sleep.” While the nature of crime, risks, and threats has remained remarkably consistent, the velocity and technological advancements have transformed their impact and scale. And without a clear return to first principles, organizations risk building security programs that are fast, modern, overly complex – yet disconnected from their true purpose.
“True efficacy emerges when security strategies are tailored to an organization’s unique mission. Founders and CEOs establish a master objective, which astute firms pursue with unwavering and untiring focus,” said Zahran.
In the United States, Pinkerton is among the few long-standing companies that have endured the test of time. With a legacy spanning 175 years, it may still be in its infancy compared to some of the oldest organizations worldwide. And like those organizations, we learned from our successes and failures. These enduring lessons remind us to prioritize core objectives and organizational values, human judgment and intuition, and adaptability and agility, ensuring security remains a strategic enabler of success and resilience, protecting what matters most.





