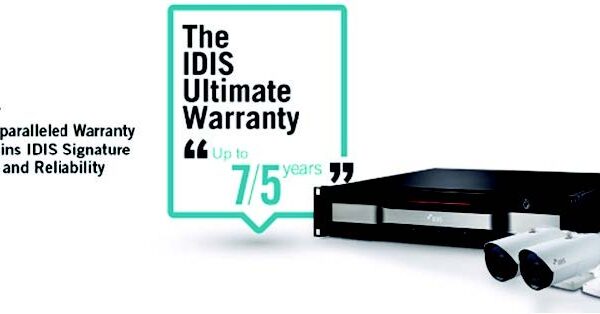
Leading Video Surveillance Warranty
New warranty extensions bring IDIS product guarantees to as many as seven years As part of the global surveillance powerhouse’s year-long 20th anniversary celebration, IDIS announced an industry-leading ‘IDIS Ultimate Warranty.’ In a landscape with average industry warranties ranging from three to five years, the new IDIS Ultimate Warranty extends the company’s standard warranties for recorders from three to five years, while adding additional extensions of the manufacturer’s guarantees for its latest-generation technologies by two years, bringing the warranty for IDIS’s H.265 network video recorders (NVRs) and multi-format HD-TVI IDIS DirectCX TVRs to an unprecedented seven years. (IDIS cameras eligible for the two-year extension will see their guarantees extend to five years.) The IDIS Ultimate Warranty gives IDIS integrators and installers a clear competitive advantage and delivers increased peace of mind with a lower cost of ownership to end users. The IDIS Ultimate Warranty is also particularly competitive when compared to PC-based solutions that typically handle up to 64 channels, which have a maximum warranty of three years, forcing end users to purchase additional warranty long before the end of the lifecycle of their surveillance solution. A recent survey conducted by IFSEC Global shows that most organizations look to upgrade surveillance systems after five to seven years. With the IDIS Ultimate Warranty, end users can be confident that their IDIS solution will be supported for its entire life cycle, a demonstration of IDIS’s confidence in its industry-leading quality and reliability. Andrew Myung, President of IDIS America, noted, “IDIS has a long reputation for bringing new and innovative products to market. Each time we do, we guarantee that each element has been designed and manufactured in-house by IDIS with quality and reliability at the forefront. We’re proud to still have IDIS DVRs in operation after more than 13 years and that they have required little to no maintenance. It’s because of our confidence in this quality and reliability that the IDIS Ultimate Warranty is a natural step. It was not a difficult choice to extend guarantees for our recorders to as many as seven years as our confidence in our products and track record as a manufacturer fully support such a move.” The IDIS Ultimate Warranty will apply to products shipped globally from July 2017 and is expected to be fully available on all covered products in the Americas by early fall.