Traditional CCTV systems use a set of cameras and a local network to connect these cameras to a video management software. The video management system typically runs on a network video recorder (NVR) or a digital video recorder (DVR). The fundamental difference between the two – NVR records IP cameras while DVR records analog cameras connected via coaxial cables, hence a DVR system would not require a network but connect cameras to the DVR as point to point connections.
In traditional CCTV system, monitoring is done by using a central monitoring system where human beings would watch multiple screens to make security-based decisions and take appropriate actions. With the technology advancement to IP, most of the earlier DVR systems have been replaced by NVR systems. This is because the IP cameras can be controlled remotely, and more importantly, they produce a digital video stream. The video stream could be in a raw or compressed form to save bandwidth as well asstorage space. Both network bandwidth and storage space are of premium significance and hence they need to be optimized for cost considerations.
Analog video streams cannot be processed by software unless they are converted into a digital stream, and in the conversion process from analog to digital video, detail, color and resolution are lost from the original analog video stream. Many deployments use this technique to process video because it is cheaper than replacing the existing system with an IP system. This is a trade-off between cost and losing key video data that could have been otherwise processed accurately to build a superior video surveillance system. Any green field project should implement an IP system as the flexibility, long term costs and future scalability of the system are at stake.
For the corporate business and high security installations such as nuclear power stations, hydro-electric power generators, airports, highway monitoring systems etc., an NVR based system is no longer an option because of its limited ability to scale. If the software processing engine is a server-based system then the scaling of the surveillance system is easily solved. A server gives one the option of building a custom solution based on the project requirements by including other surveillance and security software and hardware components besides cameras. These can be integrated into the VMS easily to build a comprehensive surveillance and security system. The other security components are access control systems, radar, signage, facial recognition, fire alarms etc. By now one must realize that an NVR based surveillance system is incapable of providing all the features to build a comprehensive surveillance and security system.
Software components that make a comprehensive Actionable Video Intelligence System
The following diagram illustrates the various security and surveillance components that are built around a central VMS software that runs on the main server. The key points to note are as follows:
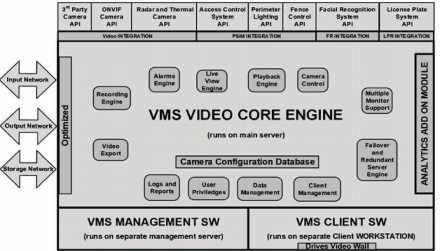
- A central VMS component.
- A VMS that runs on a separate client-server.
- A VMS client software that runs on a separate client workstation.
- The above three components are well integrated with each other.
- An optional video analytics module that is tightly coupled with the main VMS, which analyzes each video frame from a camera and executes programmed video analytics. This constitutes the basis of actionable video intelligence (AVI).
- The ability to integrate other security software components into the main VMS software core. This is accomplished using application programming interfaces (API) and a software development kit (SDK).
Popular video analytics algorithms
Following is a capture of some popular video analytics algorithms:
Motion detection
- Seamless integration of motion detection results available from cameras.
- Motion detection processing from application.
- Independent motion detection settings for every camera.
- ‘Motion detected’ and ‘No motion’ alarms to indicate start of motion and end of motion.
- Advanced motion detection algorithm with high accuracy and low resource utilization. ● Record on motion.
- Motion detection meta-data overlay on videos with configuration for overlay level – no overlay, only motion indicator, motion grids, full overlay.
- Option to exclude motion detection alarms from alarms database entries.
Video analytics
- Video analytics on IR cameras and thermal cameras.
- Support for video analytics on PTZ cameras, while the camera is in ‘home’ position. Video analytics is automatically disabled when camera moves from the home position and video analytics is automatically started when camera is moved back to home position.
- Seamless integration of video analytics module as video analytics is not a separate software application. No manual synchronization and maintenance is needed.
- Dedicated video analytics screen to display analyzed videos from multiple cameras, with analytics meta-data overlay.Quick access to video analytics settings for each camera.
- Independent video analytics settings for every camera.
- Easy to manage, tightly integrated simple user interface.
- Enhanced algorithms which need only few parameters to be configured to get good results from video analytics in most of the deployment situations. Advanced parameters are available to handle special situations.
- Local or remote processing of video analytics.
- Availability of wide range of standard analytics features.
Intrusion detection
- Wrong direction movement detection.
- Line crossing/ trip-wire.
- Camera tamper/ scene change detection.
Crowd detection
- Un-attended object detection.
- Queue length detection.
- Asset protection.
- Loitering detection.
- Tailgating detection.
- Object stopped detection.
- People counting, Vehicles counting.
- Object trace/ travel path.
- Object speed calculation.
- Digital auto-tracking.
- Vibration removal.
- Flexible architecture to quickly support customized video analytics features.
- Option of project specific combined analytics on data generated by multiple external devices and video streams.
- Option to use 3rd party video analytics libraries using their SDKs.
VMS integration techniques
There are several challenges when it comes to integrating several diverse security components with one another such as integrating several diverse software stacks e.g., ALPR, FR, PIDS (including radar/ thermal cameras), ACS, IVAS, VMS, and others.
VMS integration needs following points to take into consideration such as:
Assess integration cost
- Integration is an expensive and time-consuming process.
- Establish performance and functionality metrics for all vendors.
- Establish due diligence process to assess impact to first deployment.
Ensure seamless integration of all security components
- The integrated system should work seamlessly.
- No change to any core software stack proven in the field
VMS performance under load
- Video pixelization, jitter and frame drop.
Integration example 1: In this example a 3rd party software is used to tie up all the independent proven software stacks. A careful assessment must be made about time and cost when this technique is employed.
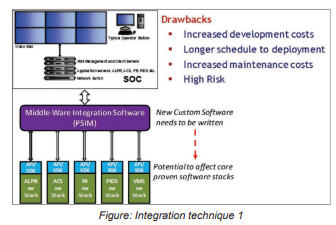
Integration example 2: In this technique the core VMS software is used as an integration point, which is possible if the radar software has been properly integrated with the VMS – as some radar manufacturers state, and which must be verified during detailed engineering design – and if the VMS software incorporates a mapping application (also assured by leading VMS suppliers).
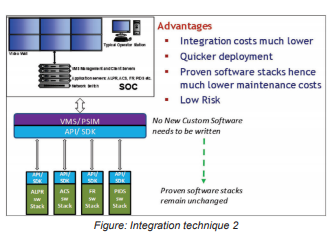
The extended VMS approach is a highly desirable starting design point, as it avoids the schedule risks, costs, and complexities of having to use a PSIM.
Understanding the cost impact of running Actionable Video Intelligence
Several analytics can be performed at the same time on the camera and the attached server. This yields 4 combinations, each to be so programmable that the end user is able to fine tune the system.
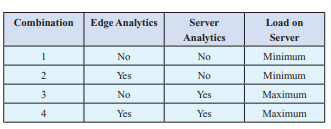
Edge analytics are relatively simple compared to the analytics that are performed on the attached server, but server analytics are more manageable and avoid application firmware updating problems including protocol conflicts and associated operational problems.
The server analytics algorithms are fairly complex and vary in performance from vendor to vendor. The decision process becomes even more complex as each vendor does not provide all the required analytics. In this case more than one vendor may be required to meet the project requirements.
Best in class vendors can be identified for the project requirements and integrate that software with the rest of the system using either integration technique 1 or integration technique 2.
For smaller deployments with less than 200 cameras, assigning all servers to run IVAS software makes the system design simpler but increases the cost and runs the risk of false alarms.
For larger deployments with more than 200 cameras, there will be a much higher risk of false alarms and a higher cost of fine tuning each camera to perform the required analytic. In real world scenarios it takes as many as 8 hours per camera to fine tune all the analytic parameters correctly to get the desired result.
