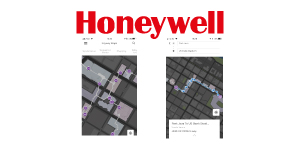
Honeywell Vector Occupant App
Honeywell has recently added new capabilities to the Honeywell Vector Occupant App that give occupants more control over their experiences within a building with the swipe of a screen. The most significant new feature is indoor navigation, which uses GPSlike technology to help users find their way around complex buildings that are difficult to navigate without directions. The benefits of the indoor navigation feature have been demonstrated in the Minneapolis Skyway System, a complex interlinked network of enclosed pedestrian walkways spanning 80 city blocks. The walkways protect Minnesotans from the harsh winter elements and summer humidity, allowing them to comfortably walk between more than 30 buildings in downtown Minneapolis. “For anyone who’s not a local, and for even some who are, finding your way around the skyway system can be a big challenge,” said Steve Cramer, President and CEO, Minneapolis Downtown Council, “With our initial use of the Honeywell Vector Occupant App, we’ve seen an immediate impact. The interactive map makes it really easy and intuitive to know exactly where you’re going, and how to get there.” In addition to the indoor navigation feature, the app also now includes a location-based feature to rate spaces, allowing those within a building to highlight comfort issues to building staff for quick resolution. Both features combine the convenience of today’s mobile devices with Internet of Things (IoT) building connectivity to help improve a user’s experience inside a building. “Much of a building’s success hinges on how happy and satisfied its occupants are. They’re the lifeblood of an organization, and their experience within a building is what keeps them coming back,” said Aseem Joshi, Country General Manager, Honeywell Building Solutions, India, “The Honeywell Vector Occupant App has given users more power to shape their building experiences from their smartphones. Now, we’re adding even more features to deepen the connections between occupants and the spaces around them so they can be as comfortable as possible, and can more easily and efficiently move about a building.” Indoor navigation Enabled by strategic partner Insiteo’s indoor location solution for smart buildings, the indoor navigation feature offers accurate indoor location, mapping, routing, presence, proximity notifications and analytics – all embedded into an integrated platform. Backed by location technology installed within a facility and software, the app’s indoor navigation provides easy-to-use way finding, with turn-by-turn voice assistance and location accuracy up to five feet. The app promotes better collaboration and improved safety via its ‘share my location’ feature, which gives users a way to more easily find each other in a building. For building owners and managers, in addition to promoting occupant satisfaction, the app also provides insights into foot traffic patterns, which building personnel can use to better inform measures like messaging placement to better serve their occupants. Location based space rating The rating feature builds on the app’s original one-click hot/ cold call capability, which lets users raise comfort issues with building personnel for resolution. Building owners and managers can view ratings and feedback on dashboards to pinpoint where building spaces need attention and improvements. They can also visualize longer-term trends and space rankings to uncover patterns and improvement opportunities to promote occupant comfort, satisfaction and productivity. Vector occupant App capabilities The new capabilities build on the Honeywell Vector Occupant App’s base functionality, which includes digital identification, mobile access control and the ability to communicate temperature discomfort to prompt adjustments by facility teams. The Honeywell Vector Occupant App is part of Honeywell’s connected services portfolio, which leverages the connectivity of buildings to improve how they operate and the experiences they offer for those who visit and work within them. The Honeywell Vector Occupant App works with Apple and Android products.