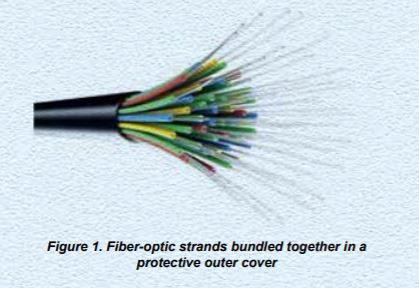
In network video, copper cables (twisted-pair) have traditionally been used to connect the camera with the control center or the recording unit. In long-range surveillance installations, however, fiber-optic cabling can be a more cost-efficient alternative. Even though it is more expensive per meter, the superior transmission characteristics of a fiber-optic cable reduces the need for expensive signal amplifiers along the way, and makes it possible to transmit more data at a time. This white paper explains what fiber-optic communication is and how it can be used in network video. It also outlines how the Axis product line is designed to support fiber-optic communication. What is fiber-optic communication? In fiber-optic communication, light signals are transmitted through glass fibers. Light reflections within a strand of glass The fibers inside a fiber-optic cable are flexible, transparent strands of very pure glass or plastic. The core of a fiber is radially enclosed by another transparent material with slightly different characteristics, the cladding. This structure makes the fiber function as a ‘light pipe,’ so that light that enters the core at one end can emerge from the other end, even when the fiber is bent or twisted. For stability and protection, the core and cladding are normally enclosed by several protective coatings, as seen in Figure 1. Whenever the light inside the fiber hits the boundary between the core and the cladding, the light will bounce in a controlled manner and essentially continue forward, bouncing back and forth between the ‘walls’ (see Figure 2). It is as if the cladding was lined with mirrors. Hardly any light is absorbed by the cladding, which is why the fiber can carry the light across great distances with nearly preserved intensity. Single-mode and multi-mode fibers Fibers come in two types, suitable for different light sources and different transmission distances. Single-mode fibers have thin cores, about 8μm in diameter, and transmit infrared laser light (wavelength = 1,300 to 1,550nm). They are usually made of glass. Single-mode fibers support only one propagation path, or mode, and are used for communication links longer than 1km. They are typically used in10-/100Mbit/s network connections spread out over extended areas. Multi-mode fibers have a larger core diameter, typically 50-100μm, and transmit infrared LED (light emitting diode) light (wavelength = 850 to 1,300nm). They are usually made of plastic-clad silica or plastic. Multi-mode fibers support many propagation paths, or modes. They are used for short-distance communication links (up to 5km), and for applications where high power must be transmitted. Duplex and simplex transmission You can transmit either two signals (full duplex) or just one signal (simplex) through one fiber-optic strand. With duplex transmission, the transmitted signal and the received signal travel through the same strand. This means that in each fiber-optic strand there are two rays of light, traveling in opposite directions at the same time (see top part of Figure 4). In simplex transmission, there is only one ray of light traveling through each fiber strand. The received signal must then travel through a second strand (see lower part of Figure 4). Duplex transmission requires only half the number of fiber strands to transmit the same amount of data compared with simplex transmission. Why use fiber-optic communication? The most common purposes of using fiber-optic connections are illumination, communication, and medical or industrial endoscopy where many fibers are bundled together to transmit an image. For telecommunications such as network video, the light traveling through the fiber is, of course, not just random light, but rather data streams encoded as light signals. Fiber-optic connections have been used for data transmission since the 1970s, but the techniques for both transmitting of the data and for manufacturing of the fiber-optic equipment have advanced drastically over the years. Long-range installations at low cost As we have seen, a fiber-optic cable can carry a signal across great distances with only very low attenuation. For a twisted-pair copper cable to be able to carry a signal across the same distance, the signal would have to be amplified at several instances along the way. This could be done using so-called repeaters, but these are rather costly. This is why fiber-optic cables can be a cost-efficient solution at long distances, even though they are more expensive per meter than copper cables. The maximum length of a fiber-optic cable ranges from 10km to 70km, depending on the type of fiber. The maximum length of a twisted-pair copper cable is 100m. Depending on the type of fiber-optic cables used, data rates can range up to 10,000Mbit/s. The cost-efficiency of fiber-optic installations is also due to the slenderness of the fibers. This means that more fibers can be bundled into a given-diameter cable. This allows more data to go over the same cable, and makes fiber-optic cables ideal for carrying digital information. No electrical interference Transmission through twisted-pair copper cables is susceptible to electromagnetic interference (EMI). This is when external electromagnetic fields affect the current in the cable, and may cause substantial problems with data loss. Fiber-optic cables, however, are immune to such interference. Also, the signal in one fiber does not interfere with those in other fibers in the same cable. Because the signal in a fiber-optic cable does not give rise to any electromagnetic field outside of the fiber, there is no signal leakage. This means that the transmission cannot be tapped, or accessed by unauthorized people. Fiber-optic communication in network video Axis offers a range of network video products that support fiber-optic communication. The key component in connecting a surveillance system with a fiber-optic cable is the SFP (small form factor pluggable) module. Other components are media converters and network cameras with integrated SFP slots. Overview of fiber-based network video system Figure 5 shows an example of a video surveillance system where a fiber-optic cable connects the sending side with the receiving side. Sending side On the sending side of the system is a network camera (in this case AXIS Q3615-VE network camera) which provides video data to be transmitted. The…